Tom Madsen – författare
Visar alla böcker från författaren Tom Madsen. Handla med fri frakt och snabb leverans.
7 produkter
7 produkter
322 kr
Skickas inom 5-8 vardagar
1 280 kr
Skickas inom 10-15 vardagar
In this book the author draws inspiration from Sun Tzu's Art of War, a work that explains conflict between nations, and he applies this to the computer security setting, examining how we should consider protecting information systems from accidents or malicious attacks. The author first briefly introduces Sun Tzu.
1 280 kr
Skickas inom 10-15 vardagar
In this book the author draws inspiration from Sun Tzu's Art of War, a work that explains conflict between nations, and he applies this to the computer security setting, examining how we should consider protecting information systems from accidents or malicious attacks. The author first briefly introduces Sun Tzu.
292 kr
Skickas inom 3-6 vardagar
615 kr
Skickas inom 10-15 vardagar
Security Architecture, or Enterprise Information security architecture, as it was originally coined by Gartner back in 2006, has been applied to many things and different areas, making a concrete definition of security architecture a difficult proposition. But having an architecture for the cyber security needs of an organization is important for many reasons, not least because having an architecture makes working with cyber security a much easier job, since we can now build on a, hopefully, solid foundation. Developing a security architecture is a daunting job for almost anyone, and in a company that has not had a cyber security program implemented before, the job becomes even harder. The benefits of having a concrete cyber security architecture in place cannot be overstated! The challenge here is that a security architecture is not something that can stand alone, it absolutely must be aligned with the business in which it is being implemented.This book emphasizes the importance, and the benefits, of having a security architecture in place. The book will be aligned with most of the sub-frameworks in the general framework called SABSA, or Sherwood Applied Business Security Architecture. SABSA is comprised of several individual frameworks and there are several certifications that you can take in SABSA. Aside from getting a validation of your skills, SABSA as a framework focuses on aligning the Security Architecture with the business and its strategy. Each of the chapters in this book will be aligned with one or more of the components in SABSA, the components will be described along with the introduction to each of the chapters.
1 378 kr
Skickas inom 10-15 vardagar
Security Architecture, or Enterprise Information security architecture, as it was originally coined by Gartner back in 2006, has been applied to many things and different areas, making a concrete definition of security architecture a difficult proposition. But having an architecture for the cyber security needs of an organization is important for many reasons, not least because having an architecture makes working with cyber security a much easier job, since we can now build on a, hopefully, solid foundation. Developing a security architecture is a daunting job for almost anyone, and in a company that has not had a cyber security program implemented before, the job becomes even harder. The benefits of having a concrete cyber security architecture in place cannot be overstated! The challenge here is that a security architecture is not something that can stand alone, it absolutely must be aligned with the business in which it is being implemented.This book emphasizes the importance, and the benefits, of having a security architecture in place. The book will be aligned with most of the sub-frameworks in the general framework called SABSA, or Sherwood Applied Business Security Architecture. SABSA is comprised of several individual frameworks and there are several certifications that you can take in SABSA. Aside from getting a validation of your skills, SABSA as a framework focuses on aligning the Security Architecture with the business and its strategy. Each of the chapters in this book will be aligned with one or more of the components in SABSA, the components will be described along with the introduction to each of the chapters.
657 kr
Skickas inom 10-15 vardagar
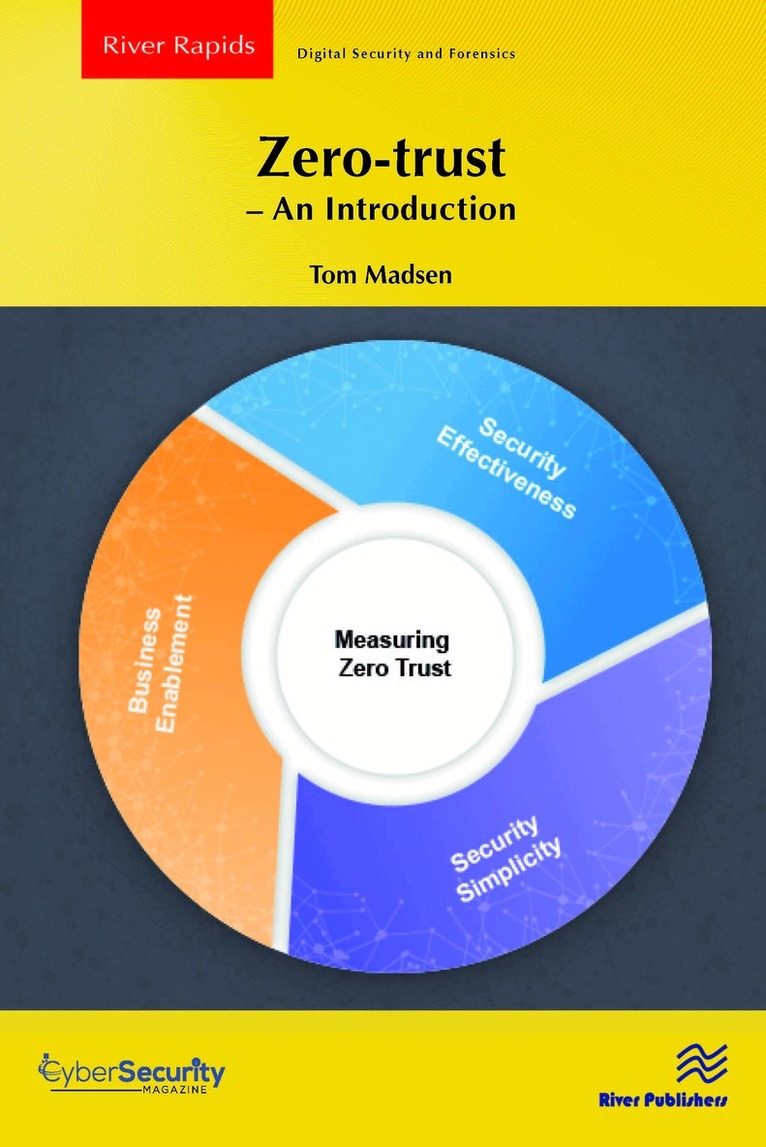
The book provides you with information on how to implement and manage a zero-trust architecture across these different layers of an infrastructure. It is an introduction to the overall purpose of zero-trust and the benefits that zero-trust can bring to an infrastructure, across many different technologies:CloudNetworkingIdentity managementOperational Technology (OT)5GZero-trust is not a product, but a way of thinking about design and architecture. Cisco and Microsoft are used as the technology vendors, but the steps and information are equally applicable to other technology vendors.