Now Publishers – serie
Visar alla böcker i serien Now Publishers. Handla med fri frakt och snabb leverans.
3 produkter
3 produkter
1 024 kr
Skickas inom 5-8 vardagar
The ebook edition of this title is Open Access and freely available to read online.The method of sparsity has been attracting a lot of attention in the fields related not only to signal processing, machine learning, and statistics, but also systems and control. The method is known as compressed sensing, compressive sampling, sparse representation, or sparse modeling. More recently, the sparsity method has been applied to systems and control to design resource-aware control systems. This book gives a comprehensive guide to sparsity methods for systems and control, from standard sparsity methods in finite-dimensional vector spaces (Part I) to optimal control methods in infinite-dimensional function spaces (Part II).The primary objective of this book is to show how to use sparsity methods for several engineering problems. For this, the author provides MATLAB programs by which the reader can try sparsity methods for themselves. Readers will obtain a deep understanding of sparsity methods by running these MATLAB programs.Sparsity Methods for Systems and Control is suitable for graduate level university courses, though it should also be comprehendible to undergraduate students who have a basic knowledge of linear algebra and elementary calculus. Also, especially part II of the book should appeal to professional researchers and engineers who are interested in applying sparsity methods to systems and control.
1 236 kr
Skickas inom 5-8 vardagar
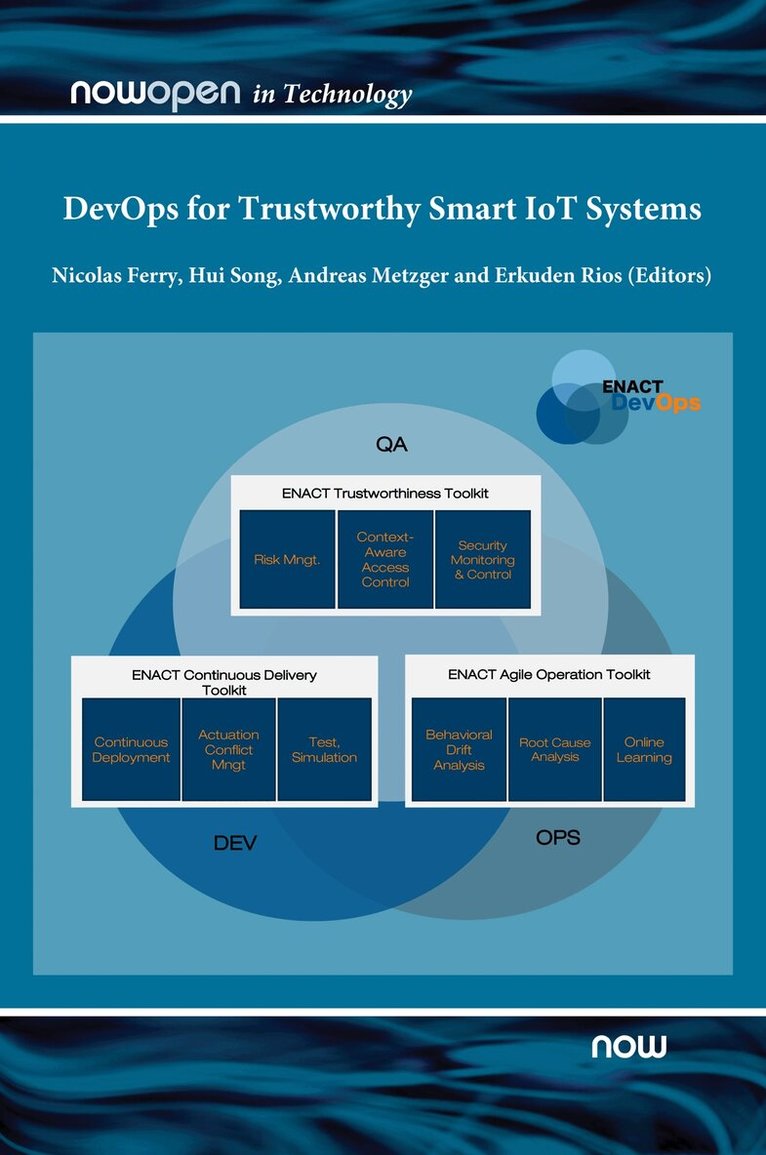
The ebook edition of this title is Open Access and freely available to read online.ENACT is a research project funded by the European Commission under its H2020 program. The project consortium consists of twelve industry and research member organisations spread across the whole EU.The overall goal of the ENACT project was to provide a novel set of solutions to enable DevOps in the realm of trustworthy Smart IoT Systems. Smart IoT Systems (SIS) are complex systems involving not only sensors but also actuators with control loops distributed all across the IoT, Edge and Cloud infrastructure. Since smart IoT systems typically operate in a changing and often unpredictable environment, the ability of these systems to continuously evolve and adapt to their new environment is decisive to ensure and increase their trustworthiness, quality and user experience. DevOps has established itself as a software development life-cycle model that encourages developers to continuously bring new features to the system under operation without sacrificing quality.This book reports on the ENACT work to empower the development and operation as well as the continuous and agile evolution of SIS, which is necessary to adapt the system to changes in its environment, such as newly appearing trustworthiness threats.
Security Technologies and Methods for Advanced Cyber Threat Intelligence, Detection and Mitigation
Inbunden, Engelska, 2022
1 024 kr
Skickas inom 5-8 vardagar
The ebook edition of this title is Open Access and freely available to read online.The rapid growth of the Internet interconnectivity and complexity of communication systems has led us to a significant growth of cyberattacks globally often with severe and disastrous consequences. The swift development of more innovative and effective (cyber)security solutions and approaches are vital which can detect, mitigate and prevent from these serious consequences. Cybersecurity is gaining momentum and is scaling up in very many areas. This book builds on the experience of the Cyber-Trust EU project’s methods, use cases, technology development, testing and validation and extends into a broader science, lead IT industry market and applied research with practical cases. It offers new perspectives on advanced (cyber) security innovation (eco) systems covering key different perspectives. The book provides insights on new security technologies and methods for advanced cyber threat intelligence, detection and mitigation. We cover topics such as cyber-security and AI, cyber-threat intelligence, digital forensics, moving target defense, intrusion detection systems, post-quantum security, privacy and data protection, security visualization, smart contracts security, software security, blockchain, security architectures, system and data integrity, trust management systems, distributed systems security, dynamic risk management, privacy and ethics.