Subhamoy Maitra – författare
Visar alla böcker från författaren Subhamoy Maitra. Handla med fri frakt och snabb leverans.
10 produkter
10 produkter
936 kr
Skickas inom 10-15 vardagar
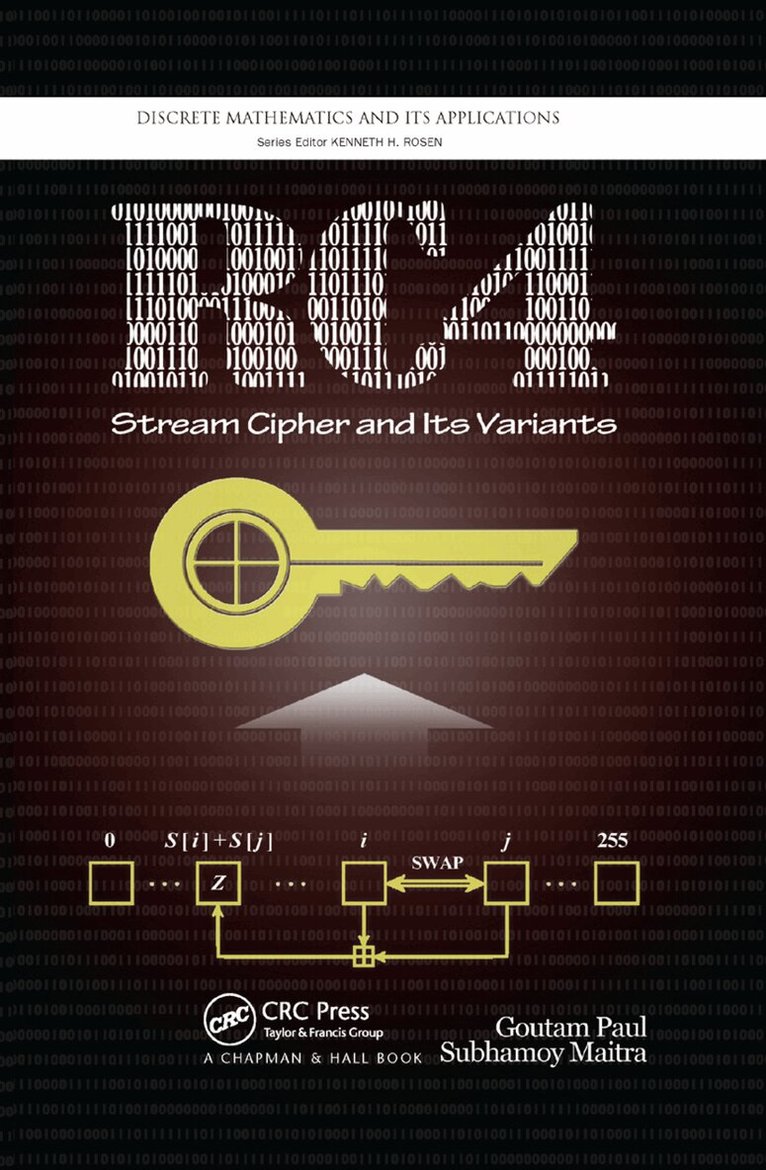
RC4 Stream Cipher and Its Variants is the first book to fully cover the popular software stream cipher RC4. With extensive expertise in stream cipher cryptanalysis and RC4 research, the authors focus on the analysis and design issues of RC4. They also explore variants of RC4 and the eSTREAM finalist HC-128.After an introduction to the vast field of cryptology, the book reviews hardware and software stream ciphers and describes RC4. It presents a theoretical analysis of RC4 KSA, discussing biases of the permutation bytes toward secret key bytes and absolute values. The text explains how to reconstruct the secret key from known state information and analyzes the RC4 PRGA in detail, including a sketch of state recovery attacks. The book then describes three popular attacks on RC4: distinguishing attacks, Wired Equivalent Privacy (WEP) protocol attacks, and fault attacks. The authors also compare the advantages and disadvantages of several variants of RC4 and examine stream cipher HC-128, which is the next level of evolution after RC4 in the software stream cipher paradigm. The final chapter emphasizes the safe use of RC4. With open research problems in each chapter, this book offers a complete account of the most current research on RC4.
2 680 kr
Skickas inom 10-15 vardagar
RC4 Stream Cipher and Its Variants is the first book to fully cover the popular software stream cipher RC4. With extensive expertise in stream cipher cryptanalysis and RC4 research, the authors focus on the analysis and design issues of RC4. They also explore variants of RC4 and the eSTREAM finalist HC-128.After an introduction to the vast field of cryptology, the book reviews hardware and software stream ciphers and describes RC4. It presents a theoretical analysis of RC4 KSA, discussing biases of the permutation bytes toward secret key bytes and absolute values. The text explains how to reconstruct the secret key from known state information and analyzes the RC4 PRGA in detail, including a sketch of state recovery attacks. The book then describes three popular attacks on RC4: distinguishing attacks, Wired Equivalent Privacy (WEP) protocol attacks, and fault attacks. The authors also compare the advantages and disadvantages of several variants of RC4 and examine stream cipher HC-128, which is the next level of evolution after RC4 in the software stream cipher paradigm. The final chapter emphasizes the safe use of RC4. With open research problems in each chapter, this book offers a complete account of the most current research on RC4.
Progress in Cryptology -- INDOCRYPT 2003
4th International Conference on Cryptology in India, New Delhi, India, December 8-10, 2003, Proceedings
Häftad, Engelska, 2003
551 kr
Skickas inom 10-15 vardagar
TheINDOCRYPTconferenceseriesstartedin2000,andINDOCRYPT2003was the fourth one in this series. This series has been accepted by the international research community as a forum for presenting high-quality crypto research, as is evident from the 101 submissions this year, spread over 21 countries and all ?ve continents. The accepted papers were written by authors from 16 countries, covering four continents. A total of 101 papers were submitted for consideration to the program c- mittee, and after a careful reviewing process 30 were accepted for presentation. One of the conditionally accepted papers was withdrawn by the authors as they found an errorin the paper that could not be repairedin the short time between the noti?cation of the reviewand the ?nalversionsubmission.Thus the ?nal list contains29acceptedpapers.Wewouldliketo thanktheauthorsofallsubmitted papers, including both those that wereaccepted and those which, unfortunately, could not be accommodated. The reviewing process for INDOCRYPT was very stringent and the schedule was extremely tight. The program committee members did an excellent job in reviewing and selecting the papers for presentation.During the review process, theprogramcommitteememberscommunicatedusingareviewsoftwarepackage developed by Bart Preneel, Wim Moreau and Joris Claessens. We acknowledge them for providing this software. These proceedings include the revised versions of the 29 selected papers. Revisions were not checkedby the programcommittee and the authors bear the full responsibility for the contents of the respective papers. Our thanks go to all the program committee members and the external reviewers(alistofthem isincludedintheproceedings)whoputintheirvaluable time and e?ort in providing important feedback to the authors.
Progress in Cryptology - INDOCRYPT 2005
6th International Conference on Cryptology in India, Bangalore, India, December 10-12, 2005, Proceedings
Häftad, Engelska, 2005
551 kr
Skickas inom 10-15 vardagar
Indocrypt began in the year 2000 under the leadership of Bimal Roy and - docrypt 2005 was the sixth conference in this series. This series has been well accepted by the international research community as a forum for presenting high-quality cryptography research. This year a total of 148 papers were s- mitted for consideration to the Program Committee and after a careful review process, 31 were accepted for presentation. We would like to thank the authors of all submitted papers, including those that were accepted and those which, unfortunately, could not be accommodated. ThereviewingprocessforIndocryptwasverystringentandtheschedulewas- tremelytight.TheProgramCommitteemembersdidanexcellentjobinreviewing andselectingthepapersforpresentation.Duringthereviewprocess,theProgram Committee members were communicating using a review software developed by BartPreneel,WimMoreauandJorisClaessens.Weacknowledgethemforprov- ingthesoftware.ThesoftwarewashostedatI2R,Singaporeandwearegratefulto Feng BaoandJianyingZhouforallowingthat.Thisyear'sconferencewasdeeply indebtedto QiuYingofI2R,Singapore,who tookthe responsibilityofmainta- ing the review softwareand the server.Without his great cooperationIndocrypt 2005could nothavebeen possible.Inthis regardI wouldliketo acknowledgethe supportofTanmoyKantiDas,DibyenduChakrabarti,MridulNandi,Deepak- mar Dalai, Sumanta Sarkar and Sourav Mukhopadhyay for handling important administrativeissuesinthesubmissionandreviewprocessesaswellasforputting togethertheseproceedingsintheir?nalform.WearealsogratefultoPalashSarkar forhiscooperationandguidanceinIndocrypt2005. The proceedings include the revised versions of the 31 selected papers. Re- sions were not checked by the ProgramCommittee and the authors bear the full responsibility for the contents of the respective papers. Our thanks go to all the Program members and the external reviewers (a list of them is included in the proceedings) who put in their valuable time and e?ort in providing important feedbackto the authors.We thank V. KumarMurty ofthe UniversityofToronto for kindly agreeing to present the invited talk. The talk has been included in the proceedings.
1 422 kr
Skickas inom 10-15 vardagar
This book discusses the state-of-the-art techniques in the domain of contact tracing applications. This book provides a link between new proposals related to contact tracing applications and a contextual literature review primarily from the cryptologic viewpoint.
1 422 kr
Skickas inom 10-15 vardagar
This book discusses the state-of-the-art techniques in the domain of contact tracing applications. This book provides a link between new proposals related to contact tracing applications and a contextual literature review primarily from the cryptologic viewpoint.
Quantum Algorithms for Cryptographically Significant Boolean Functions
An IBMQ Experience
Häftad, Engelska, 2021
769 kr
Skickas inom 10-15 vardagar
This book is a timely report of the state-of-the-art analytical techniques in the domain of quantum algorithms related to Boolean functions. Topics covered in the book include Qubit, Deutsch–Jozsa and Walsh spectrum, Grover’s algorithm, Simon’s algorithm and autocorrelation spectrum.
551 kr
Skickas inom 10-15 vardagar
This book is a timely document of state-of-the art analytical techniques in the domain of stream cipher design and analysis with a specific cipher, named ZUC.
Boolean Functions: Cryptographic And Combinatorial Properties - Functions With Symmetry
Inbunden, Engelska, 2020
2 043 kr
Tillfälligt slut
This book discusses cryptographic and combinatorial properties of Boolean functions. Boolean functions are very easy to understand (but deep in analysis) and the subject covers significant amount of material in digital circuits, communication theory, VLSI design, computer science, coding theory and Mathematics. Boolean function is considered as one of the most basic building blocks in cryptographic system design. The properties that make a Boolean function suitable for a cryptographic system, are mostly combinatorial. We discuss these properties (e.g., balancedness, nonlinearity, correlation immunity, propagation characteristics, algebraic immunity) in detail. For each of the properties, existing research results and the recent contributions in the literature will be presented. The basic material will always contain hardcore theoretical results. However, we present the materials in a way that a person with undergraduate level mathematical background can access it. Implementation details related to these properties (e.g., how to check in writing a program whether a Boolean function is correlation immune) will be detailed.In addition to theoretical construction techniques for Boolean functions with different combinatorial and cryptographic properties, the book will concentrate on different state-of-the-art search techniques. In some cases these search techniques provide better results than the construction techniques for low number of input variables and they are quite interesting as the size of the complete set of Boolean functions is super exponential in the number of input variables. Different symmetries in the set of Boolean functions will also be presented in detail. The author will present the inherent beauty of Boolean functions that he has experienced in his research career.
922 kr
Skickas inom 10-15 vardagar
Dieses Buch diskutiert modernste Techniken im Bereich der Contact-Tracing-Anwendungen. Dieses in der Medizin gut bekannte Thema hat aufgrund der COVID-19-Pandemie Aufmerksamkeit von Regierungen, verschiedenen Industrien und der akademischen Welt erhalten. Das Buch stellt eine Verbindung zwischen neuen Vorschlägen zu Contact-Tracing-Anwendungen und einer Kontext-Literaturübersicht hauptsächlich aus kryptologischer Sicht her. Da diese Anwendungen die Sicherheit und Privatsphäre von Personen betreffen, ist ihre Analyse aus kryptologischer Sicht von höchster Bedeutung. Daher werden die aktuellen Entwicklungen der weltweiten Vorschläge, einschließlich Singapur, Europa, USA, Australien und Indien, diskutiert. Durch eine eingehende Untersuchung der Designprinzipien jedes Protokolls ist dieses Buch für Forscher, Studierende und Fachleute gleichermaßen wertvoll.